Refer to the exhibit.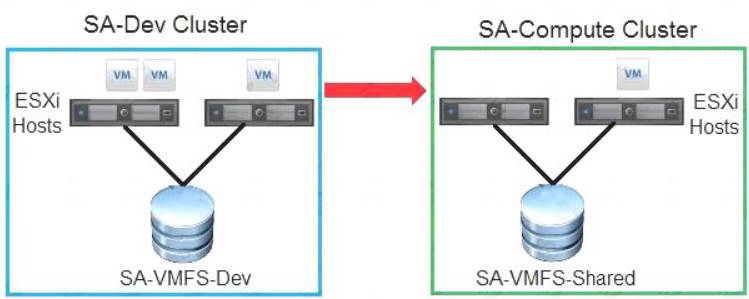
Which two migration methods can an administrator use to move virtual machines from the SA-Dev cluster to the SA-Compute cluster? (Choose two.)
Correct Answer:
CE
An administrator wants to leverage the processor-specific technology that uses a security extension for securing virtual machines (VMs). This will allow user-level code to define private regions of memory called enclaves that are protected from external access.
What does the administrator need to configure to enable VMs to use this technology? (Choose the best answer.)
Correct Answer:
B
An administrator adds an additional host to a cluster and is attempting to remediate the configuration with a host profile.
Which option would the administrator select on the host before it can be remediated with an existing host profile? (Choose the best answer.)
Correct Answer:
C
https://docs.vmware.com/en/VMware-vSphere/7.0/com.vmware.vsphere.hostprofiles.doc/GUID-09C00374-53C
ESXi provides VLAN support by assigning a VLAN ID to which component? (Choose the best answer.)
Correct Answer:
D
A vSphere environment is configured with 1 Gigabit Ethernet for vSphere vMotion. The application team is complaining that when they try to migrate a powered-on virtual machine, the progress is slow and unsuccessful the majority of the time.
Which two recommendations should the administrator make to improve vSphere vMotion performance? (Choose two.)
Correct Answer:
CD
https://docs.vmware.com/en/VMware-vSphere/6.5/com.vmware.vsphere.vm_admin.doc/GUID-254B2CE8-20A