- (Exam Topic 13)
Who is responsible for the protection of information when it is shared with or provided to other organizations?
Correct Answer:
C
Section: Security Operations
- (Exam Topic 7)
Which of the following is the FIRST step in the incident response process?
Correct Answer:
D
- (Exam Topic 9)
Which of the following is a limitation of the Common Vulnerability Scoring System (CVSS) as it relates to conducting code review?
Correct Answer:
C
- (Exam Topic 12)
Match the types of e-authentication tokens to their description.
Drag each e-authentication token on the left to its corresponding description on the right.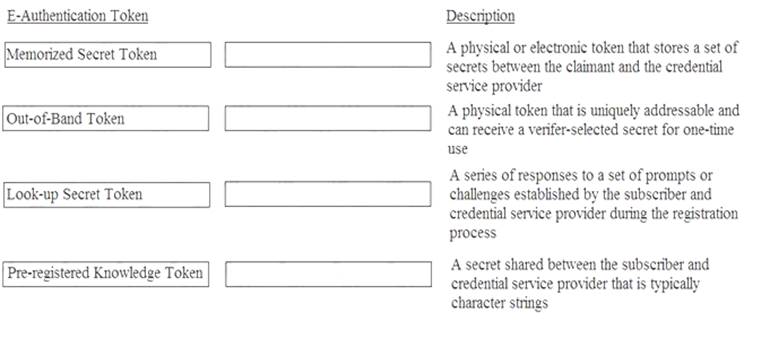
Solution:
Look-up secret token - A physical or electronic token that stores a set of secrets between the claimant and the credential service provider
Out-of-Band Token - A physical token that is uniquely addressable and can receive a verifier-selected secret for one-time use
Pre-registered Knowledge Token - A series of responses to a set of prompts or challenges established by the subscriber and credential service provider during the registration process
Memorized Secret Token - A secret shared between the subscriber and credential service provider that is typically character strings
Does this meet the goal?
Correct Answer:
A
- (Exam Topic 14)
Information security metrics provide the GREATEST value tp management when based upon the security manager’s knowledge of which of the following?
Correct Answer:
B