Refer to the exhibit, which shows a network diagram.
Which protocol should you use to configure the FortiGate cluster?
Correct Answer:
A
Given the network diagram and the presence of two FortiGate devices, the Fortinet Gate Clustering Protocol (FGCP) in active-passive mode is the most appropriate for setting up a FortiGate cluster. FGCP supports high availability configurations and is designed to allow one FortiGate to seamlessly take over if the other fails, providing continuous network availability. This is supported by Fortinet documentation for high availability configurations using FGCP.
You want to configure faster failure detection for BGP
Which parameter should you enable on both connected FortiGate devices?
Correct Answer:
B
BFD (Bidirectional Forwarding Detection) is a protocol that provides fast failure detection for BGP by sending periodic messages to verify the connectivity between two peers1. BFD can be enabled on both connected FortiGate devices by using the command set bfd enable under the BGP configuration2. References: = Technical Tip :
FortiGate BFD implementation and examples …, Configure BGP | FortiGate / FortiOS 7.0.2
- Fortinet Documentation
Refer to the exhibit, which shows a network diagram.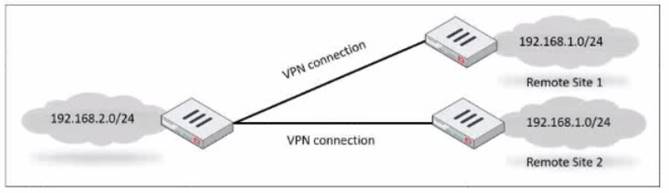
Which IPsec phase 2 configuration should you impalement so that only one remote site is connected at any time?
Correct Answer:
C
To ensure that only one remote site is connected at any given time in an
IPsec VPN scenario, you should useroute-overlapwith the option to either use-new or use- old. This setting dictates which routes are preferred and how overlaps in routes are handled, allowing for one connection to take precedence over the other (C).
References:
✑ FortiOS Handbook - IPsec VPN
Which, three conditions are required for two FortiGate devices to form an OSPF adjacency? (Choose three.)
Correct Answer:
ABE
✑ Option A is correct because the OSPF interface network types determine how the routers form adjacencies and exchange LSAs on a network segment. The network types must match for the routers to become neighbors1.
✑ Option B is correct because the OSPF router IDs are used to identify each router in the OSPF domain and to establish adjacencies. The router IDs must be unique for the routers to become neighbors2.
✑ Option E is correct because the authentication settings control how the routers authenticate each other before exchanging OSPF packets. The authentication settings must match for the routers to become neighbors3.
✑ Option C is incorrect because the OSPF interface priority settings are used to elect
the designated router (DR) and the backup designated router (BDR) on a broadcast or non-broadcast multi-access network. The priority settings do not have to be unique for the routers to become neighbors, but they affect the DR/BDR election process4.
✑ Option D is incorrect because the OSPF link costs are used to calculate the
shortest path to a destination network based on the bandwidth of the links. The link costs do not have to match for the routers to become neighbors, but they affect the routing decisions5. References: =
✑ 1: OSPF network types
✑ 2: OSPF router ID
✑ 3: OSPF authentication
✑ 4: OSPF interface priority
✑ 5: OSPF link cost
Which two statements about the Security fabric are true? (Choose two.)
Correct Answer:
BC
In the Security Fabric, only the root FortiGate sends logs to FortiAnalyzer (B). Additionally, only FortiGate devices withconfiguration-syncenabled receive and synchronize global Central Management Database (CMDB) objects that the root FortiGate sends (C). FortiGate uses the FortiTelemetry protocol to communicate with other FortiGates, not FortiAnalyzer (A). The last option (D) is incorrect as all FortiGates can collect and forward network topology information to FortiAnalyzer.
References:
✑ FortiOS Handbook - Security Fabric