- (Exam Topic 3)
You have a Microsoft Sentinel workspace named workspace1 and an Azure virtual machine named VM1. You receive an alert for suspicious use of PowerShell on VM1.
You need to investigate the incident, identify which event triggered the alert, and identify whether the following actions occurred on VM1 after the alert: The modification of local group memberships
The modification of local group memberships  The purging of event logs
The purging of event logs
Which three actions should you perform in sequence in the Azure portal? To answer, move the appropriate
actions from the list of actions to the answer area and arrange them in the correct order.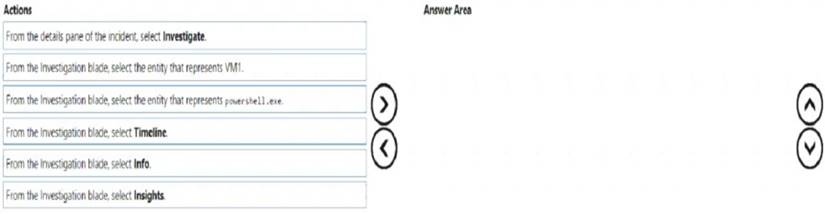
Solution:
Step 1: From the Investigation blade, select Insights
The Investigation Insights Workbook is designed to assist in investigations of Azure Sentinel Incidents or individual IP/Account/Host/URL entities.
Step 2: From the Investigation blade, select the entity that represents VM1.
The Investigation Insights workbook is broken up into 2 main sections, Incident Insights and Entity Insights. Incident Insights
The Incident Insights gives the analyst a view of ongoing Sentinel Incidents and allows for quick access to their associated metadata including alerts and entity information.
Entity Insights
The Entity Insights allows the analyst to take entity data either from an incident or through manual entry and explore related information about that entity. This workbook presently provides view of the following entity types:
IP Address Account Host
URL
Step 3: From the details pane of the incident, select Investigate. Choose a single incident and click View full details or Investigate. Reference:
https://github.com/Azure/Azure-Sentinel/wiki/Investigation-Insights---Overview https://docs.microsoft.com/en-us/azure/sentinel/investigate-cases
Does this meet the goal?
Correct Answer:
A
- (Exam Topic 2)
You need to configure the Azure Sentinel integration to meet the Azure Sentinel requirements. What should you do? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.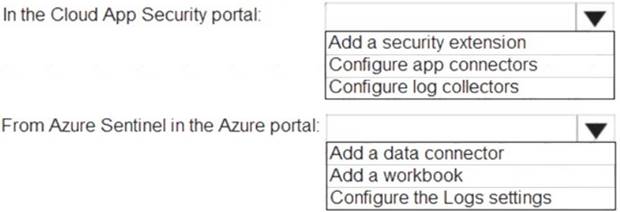
Solution:
Graphical user interface, text, application Description automatically generated
Reference:
https://docs.microsoft.com/en-us/cloud-app-security/siem-sentinel
Does this meet the goal?
Correct Answer:
A
- (Exam Topic 2)
You need to create the analytics rule to meet the Azure Sentinel requirements. What should you do? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.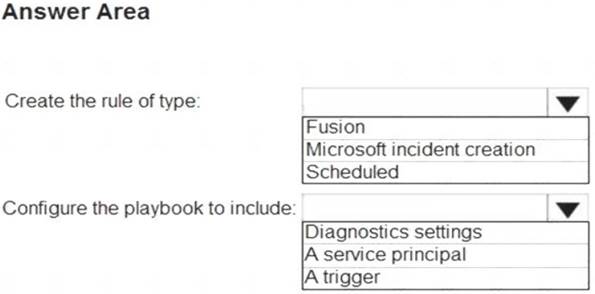
Solution: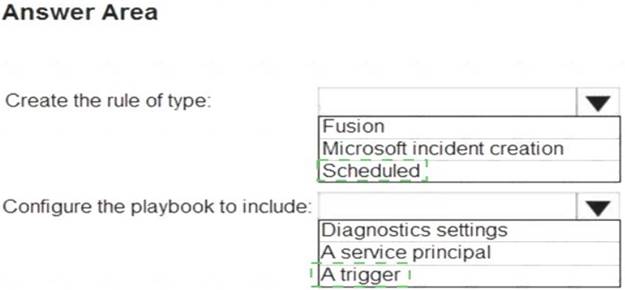
Does this meet the goal?
Correct Answer:
A
- (Exam Topic 3)
You have an Azure Storage account that will be accessed by multiple Azure Function apps during the development of an application.
You need to hide Azure Defender alerts for the storage account.
Which entity type and field should you use in a suppression rule? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.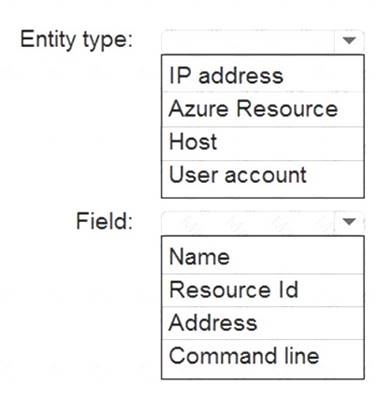
Solution:
Graphical user interface, application Description automatically generated
Reference:
https://techcommunity.microsoft.com/t5/azure-security-center/suppression-rules-for-azure-security-center-alerts
Does this meet the goal?
Correct Answer:
A
- (Exam Topic 3)
You have five on-premises Linux servers.
You have an Azure subscription that uses Microsoft Defender for Cloud. You need to use Defender for Cloud to protect the Linux servers.
What should you install on the servers first?
Correct Answer:
B
Defender for Cloud depends on the Log Analytics agent. Use the Log Analytics agent if you need to:
* Collect logs and performance data from Azure virtual machines or hybrid machines hosted outside of Azure
* Etc. Reference:
https://docs.microsoft.com/en-us/azure/defender-for-cloud/os-coverage
https://docs.microsoft.com/en-us/azure/azure-monitor/agents/agents-overview#log-analytics-agent