- (Exam Topic 4)
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to rt As a result, these questions will not appear in the review screen.
You have an Azure subscription named Sub1.
You have an Azure Storage account named Sa1 in a resource group named RG1.
Users and applications access the blob service and the file service in Sal by using several shared access signatures {SASs) and stored access policies.
You discover that unauthorized users accessed both the rile service and the blob service. You need to revoke all access to Sa1.
Solution: You regenerate the access keys. Does this meet the goal?
Correct Answer:
A
To revoke a stored access policy, you can either delete it, or rename it by changing the signed identifier. Changing the signed identifier breaks the associations between any existing signatures and the stored access
policy. Deleting or renaming the stored access policy immediately effects all of the shared access signatures associated with it.
References:
https://docs.microsoft.com/en-us/rest/api/storageservices/Establishing-a-Stored-Access-Policy
- (Exam Topic 4)
You have an Azure subscription that contains an Azure SQL database named SQL1. You plan to deploy a web app named App1.
You need to provide App1 with read and write access to SQL1. The solution must meet the following requirements: Provide App1 with access to SQL1 without storing a password.
Provide App1 with access to SQL1 without storing a password.  Use the principle of least privilege.
Use the principle of least privilege. Minimize administrative effort.
Minimize administrative effort.
Which type of account should App1 use to access SQL1, and which database roles should you assign to App1? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.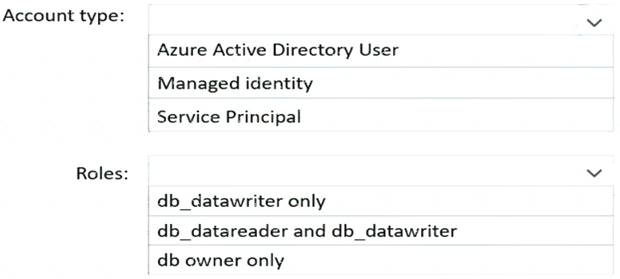
Solution:
Graphical user interface, text, application Description automatically generated
Reference:
https://docs.microsoft.com/en-us/azure/app-service/tutorial-connect-msi-sql-database?tabs=windowsclient,d
Does this meet the goal?
Correct Answer:
A
- (Exam Topic 4)
You need to create an Azure key vault. The solution must ensure that any object deleted from the key vault be retained for 90 days.
How should you complete the command? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.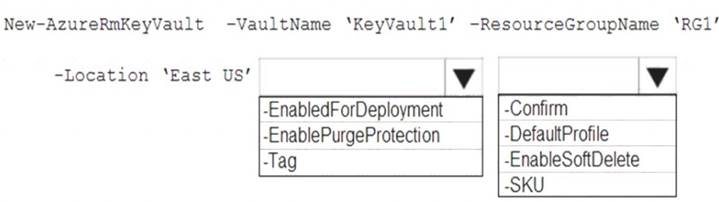
Solution:
Box 1: -EnablePurgeProtection
If specified, protection against immediate deletion is enabled for this vault; requires soft delete to be enabled as well.
Box 2: -EnableSoftDelete
Specifies that the soft-delete functionality is enabled for this key vault. When soft-delete is enabled, for a grace period, you can recover this key vault and its contents after it is deleted.
References:
https://docs.microsoft.com/en-us/powershell/module/azurerm.keyvault/new-azurermkeyvault
Does this meet the goal?
Correct Answer:
A
- (Exam Topic 4)
You need to create a new Azure Active Directory (Azure AD) directory named 10317806.onmicrosoft.com. The new directory must contain a user named user10317806 who is configured to sign in by using Azure Multi-Factor Authentication (MFA).
Solution:
To create a new Azure AD tenant:
* 1. Browse to the Azure portal and sign in with an account that has an Azure subscription.
* 2. Select the plus icon (+)
and search foAr zure Active Directory.
* 3. Select Azure Active Directory
in the search results.
* 4. Select Create.
* 5. Provide an Organization name
This will create the directory named 10317806.onmicrosoft.com.
(10317806) and anInitial domain name (10317806). Then select Create.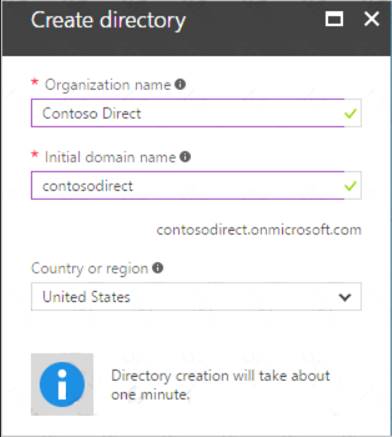
* 6. After directory creation is complete, select the information box to manage your new directory. To create the user:
* 1. In the Azure portal, make sure you are on the Azure Active Directory fly out.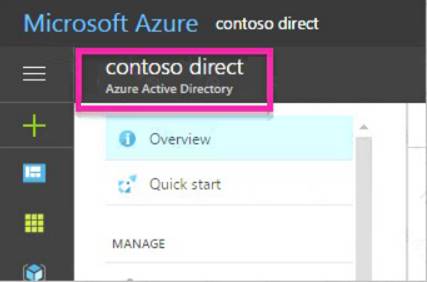
If not, select the Azure Active Directory icon from the left services navigation.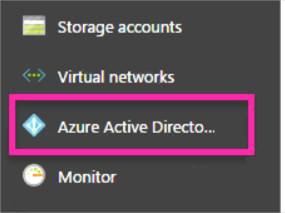
* 2. Under Manage, select Users.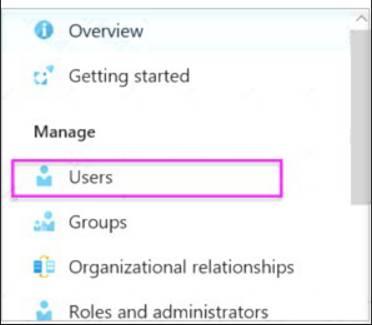
* 3. Select All users
and then selec+t New user.
* 4. Provide a Name
andUser name
(user10317806) for the user. When you're done, selecCt reate.
To enable MFA:
* 1. In the Azure portal, make sure you are on the Azure Active Directory fly out.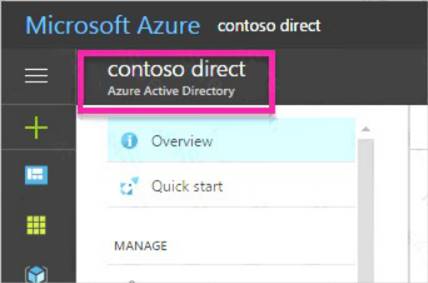
If not, select the Azure Active Directory icon from the left services navigation.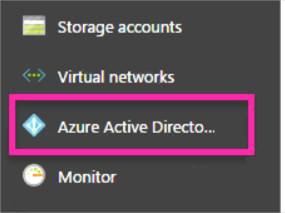
* 2. Under Manage, select Users.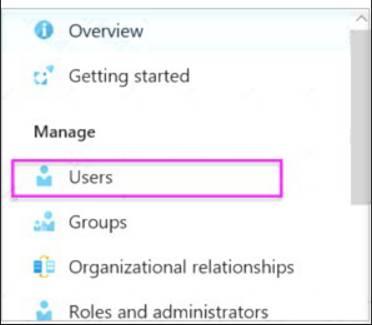
* 3. Click on the Multi-Factor Authentication link.
* 4. Tick the checkbox next to the user’s name and click the Enable link.
Reference:
https://docs.microsoft.com/en-us/power-bi/developer/create-an-azure-active-directory-tenant
Does this meet the goal?
Correct Answer:
A
- (Exam Topic 1)
You need to meet the identity and access requirements for Group1. What should you do?
Correct Answer:
D
https://docs.microsoft.com/en-us/azure/active-directory/users-groups-roles/groups-dynamic-membership Scenario:
Litware identifies the following identity and access requirements: All San Francisco users and their devices must be members of Group1.
The tenant currently contain this group: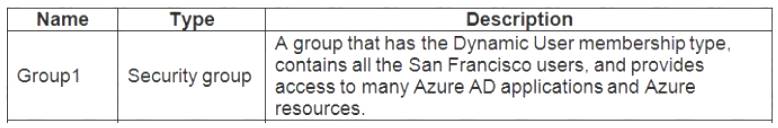
References:
https://docs.microsoft.com/en-us/azure/active-directory/users-groups-roles/groups-dynamic-membership https://docs.microsoft.com/en-us/azure/active-directory/fundamentals/active-directory-groups-create-azure-porta